|
Size: 1188
Comment:
|
Size: 2185
Comment:
|
| Deletions are marked like this. | Additions are marked like this. |
| Line 4: | Line 4: |
| == CPTR 427 Network Security Class == | = CPTR 427 Network Security Class Wiki = {{http://imgs.xkcd.com/comics/cryptography.png}} |
| Line 6: | Line 7: |
| Below is a list of subpages for NetworkSecurity | This page contains resources for Network Security CPTR 427. For assignments etc. see the [[https://eclass.e.southern.edu|Eclass website]]. For information on '''what you should already know''', take a look at [[NetworkSecurity/Prerequisites]]. |
| Line 8: | Line 9: |
| * [[NetworkSecurity/Lab]] | == Topics, Resources and Ideas for the future == * /NetworkSecurityEssentials4 notes from the book used in 2013. * [[/Lab]] * [[/Nebula]] * [[/Tools]] * [[http://academic.comptiastore.com/|CompTIA Academic Marketplace]] * [[/Programs]] * [[/Spam]] * /FireWall * [[/Topics]] * /SageIdeas * [[http://facultyfp.salisbury.edu/despickler/personal/CryptTools.asp|Cryptotools]] from AMS/MAA conference 2011 by Dr. Don Spickler. * [[http://www.backtrack-linux.org/|Backtrack Penetration Testing]] * Two proxy tools that allow editing and observing http(s) are [[NetworkSecurity/WebScarab|Web scarab]] and [[http://www.parosproxy.org/|Paros Proxy]] - there is also some nice proxies specifically for firefox. * [[http://www.securitywizardry.com/radar.htm|A nice dashboard]] * [[http://osvdb.org/|Open Source Vulnerability Database]] * [[http://web.nvd.nist.gov/view/vuln/search?execution=e2s1|National Vulnerability Database]] * [[http://exploit-db.com/]] Once upon a time there was a site called Milw0rm.com and it was great! But the maintainer passed away and eventually it was taken over by http://exploit-db.com/. * Back in the stone age (relatively speaking of course) Dr. A took a course called [[Csce877]]. |
| Line 10: | Line 29: |
| == Using WebScarab with WebGoat == | == Materials Used in this Class == '''Recommended AdditionalReading''' |
| Line 12: | Line 32: |
| 1. Start up WebScarab. It may be in basic mode. a. If it is, Go to Tools->Use Full Interface. a. Restart WebScarab. 1. Fire up IE and go to Tools->Internet Options->Connections->LAN settings. 1. Check Use proxy server and set address to localhost port 8008. 1. Click OK and OK. 1. On WebScarab go to Proxy->Manual Edit. Check Intercept Requests. Select GET and POST (using the CTRL key to select both). 1. In IE go to http://localhost./WebGoat/attack. (notice the dot after localhost, it is required to apply proxy settings on localhost.) WebScarab should already start intercepting. The lessons should work after that. I was able to do a command injection following the steps in the solution. I have now put the proxy settings back to the way they were and shut down WebGoat (for security reasons, not sure if that was necessary but I did it.) |
* [[http://www.snort.org/assets/125/snort_manual-2_8_5_1.pdf|Snort Manual]] (Free) * [[http://ofps.oreilly.com/titles/9781449320317/ch_Security.html|MVC 4 Security, Authentication and Authorization]] * [[http://www.tomsitpro.com/articles/information-security-certifications,2-205.html|Security Certifications]] |
| Line 21: | Line 36: |
| == DES Hints == | |
| Line 22: | Line 38: |
| = Often Discussed Topics = | * http://www.cs.bham.ac.uk/research/projects/lemsys/DES/DESPage.jsp |
| Line 24: | Line 40: |
| * IpSec ---- CategoryHomepage |
== Past Year Class Pages == * /Cptr427Winter2010 |
CPTR 427 Network Security Class Wiki
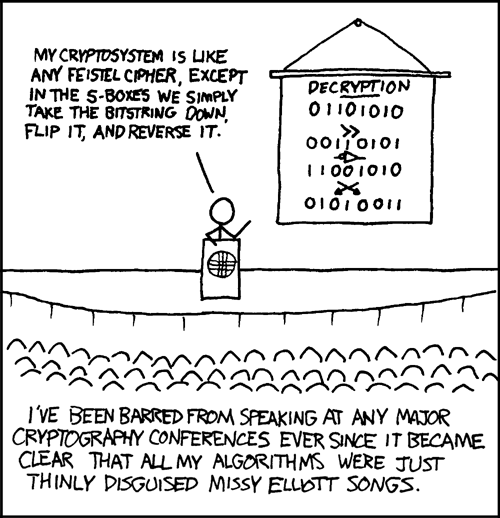
This page contains resources for Network Security CPTR 427. For assignments etc. see the Eclass website. For information on what you should already know, take a look at NetworkSecurity/Prerequisites.
Topics, Resources and Ideas for the future
/NetworkSecurityEssentials4 notes from the book used in 2013.
Cryptotools from AMS/MAA conference 2011 by Dr. Don Spickler.
Two proxy tools that allow editing and observing http(s) are Web scarab and Paros Proxy - there is also some nice proxies specifically for firefox.
http://exploit-db.com/ Once upon a time there was a site called Milw0rm.com and it was great! But the maintainer passed away and eventually it was taken over by http://exploit-db.com/.
Back in the stone age (relatively speaking of course) Dr. A took a course called Csce877.
Materials Used in this Class
Recommended AdditionalReading
DES Hints
