|
Size: 2040
Comment:
|
Size: 2619
Comment:
|
| Deletions are marked like this. | Additions are marked like this. |
| Line 4: | Line 4: |
| = CPTR 427 Network Security Class Wiki = | = CPTR 427 Network Security = |
| Line 6: | Line 6: |
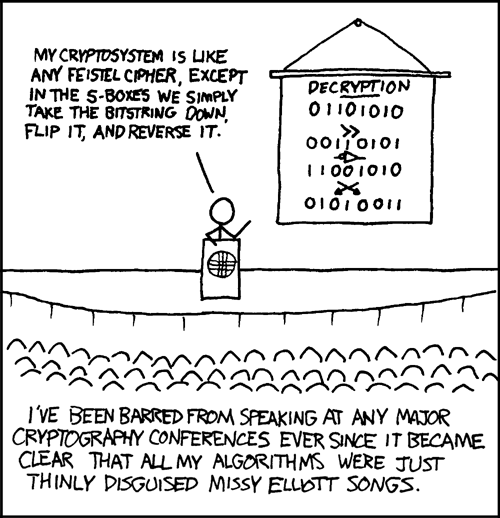
| This page contains general information about security. For your specific class check the list below: | || <<TableOfContents>> || {{http://imgs.xkcd.com/comics/cryptography.png||width=300}} || |
| Line 8: | Line 8: |
| * Cptr427Winter2010 | == Syllabus == |
| Line 10: | Line 10: |
| Every class I teach uses a standard syllabus. This [[/Syllabus|syllabus link]] contains information unique to this course. | |
| Line 11: | Line 12: |
| Before you get too involved with looking at what we plan to do this semester, you need to look at '''what you should already know'''. Take a look at [[NetworkSecurity/Prerequisites]]. | = Resources = |
| Line 13: | Line 14: |
| This page contains resources for Network Security CPTR 427. For assignments etc. see the [[https://eclass.e.southern.edu|Eclass website]]. For information on '''what you should already know''', take a look at [[NetworkSecurity/Prerequisites]]. | |
| Line 14: | Line 16: |
| == Topics, Resources and Ideas for the future == /* * /NetworkSecurityEssentials4 notes from the book used in 2013. */ * [[/Schedule|Schedule]] * [[/PassingSecurityPlus|Passing Security+ Exam - Links]] * [[/Lab]] * [[/Nebula|Nebuala, a nice beginner hacking tutorial]] * [[https://www.offensive-security.com/metasploit-unleashed/|Metasploit course - free]] * [[/Tools]] * [[http://academic.comptiastore.com/|CompTIA Academic Marketplace]] * [[/Programs]] * [[/Spam]] * /FireWall * [[/Topics]] * /SageIdeas * [[http://facultyfp.salisbury.edu/despickler/personal/CryptTools.asp|Cryptotools]] from AMS/MAA conference 2011 by Dr. Don Spickler. * [[http://www.backtrack-linux.org/|Backtrack Penetration Testing]] * Two proxy tools that allow editing and observing http(s) are [[NetworkSecurity/WebScarab|Web scarab]] and [[http://www.parosproxy.org/|Paros Proxy]] - there is also some nice proxies specifically for firefox. * [[http://www.securitywizardry.com/radar.htm|A nice dashboard]] * [[http://osvdb.org/|Open Source Vulnerability Database]] * [[http://web.nvd.nist.gov/view/vuln/search?execution=e2s1|National Vulnerability Database]] * [[http://exploit-db.com/]] Once upon a time there was a site called Milw0rm.com and it was great! But the maintainer passed away and eventually it was taken over by http://exploit-db.com/. * /SocksProxy * Back in the stone age (relatively speaking of course) Dr. A took a course called [[Csce877]]. |
|
| Line 15: | Line 40: |
| Below is a list of areas we will look at in NetworkSecurity | == Materials Used in this Class == '''Recommended AdditionalReading''' |
| Line 17: | Line 43: |
| * [[NetworkSecurity/Lab]] * [[NetworkSecurity/Tools]] * [[NetworkSecurity/Hacking]] * [[NetworkSecurity/Encryption]] * [[NetworkSecurity/FireWall]] * In the past we have used [[NetworkSecurity/WebScarab|Web scarab]] * [[http://www.securitywizardry.com/radar.htm|A nice dashboard]] |
* [[http://www.snort.org/assets/125/snort_manual-2_8_5_1.pdf|Snort Manual]] (Free) * [[http://ofps.oreilly.com/titles/9781449320317/ch_Security.html|MVC 4 Security, Authentication and Authorization]] * [[http://www.tomsitpro.com/articles/information-security-certifications,2-205.html|Security Certifications]] |
| Line 25: | Line 47: |
| == DES Hints == | |
| Line 26: | Line 49: |
| == Books Used in this Class == | * http://www.cs.bham.ac.uk/research/projects/lemsys/DES/DESPage.jsp |
| Line 28: | Line 51: |
| '''Required Books''' * [[http://www.snort.org/assets/125/snort_manual-2_8_5_1.pdf | Snort Manual]] (Free) * Hacking Exposed 6th Ed. ISBN: 978-0-07-161374-3 * Each student will be responsible for presenting a chapter from this book. * Each student will be responsible for demonstrating an attack related to the chapter they present. * The Code Book: The Science of Secrecy from Ancient Egypt to Quantum Cryptography ISBN: 0385495323 * Each student must read this New York Times Best Seller. * Cryptography will be studied in conjunction with the assigned chapters. * Cryptography and Network Security 4th Ed. ISBN: 0-13-187316-4 * The theory of cryptography (Symmetric, Public-key, Key-management, Hash and MAC) are covered from this book * Applications of theory are partially covered from this book (Kerberos, X.509, IPSec) * Dr. A will do all the lecturing on these topics. * Labs will be given from handouts and rely on internet and suggested resources. Topics will be take from [[NetworkSecurity/Lab]] '''Recommended Book(s)''' * Snort IDS and IPS Toolkit ISBN-10: 1-59749-099-7 ---- CategoryHomepage |
== Past Year Class Pages == * /Cptr427Winter2010 |
CPTR 427 Network Security
Contents
|
|
Syllabus
Every class I teach uses a standard syllabus. This syllabus link contains information unique to this course.
Resources
This page contains resources for Network Security CPTR 427. For assignments etc. see the Eclass website. For information on what you should already know, take a look at NetworkSecurity/Prerequisites.
Topics, Resources and Ideas for the future
Cryptotools from AMS/MAA conference 2011 by Dr. Don Spickler.
Two proxy tools that allow editing and observing http(s) are Web scarab and Paros Proxy - there is also some nice proxies specifically for firefox.
http://exploit-db.com/ Once upon a time there was a site called Milw0rm.com and it was great! But the maintainer passed away and eventually it was taken over by http://exploit-db.com/.
Back in the stone age (relatively speaking of course) Dr. A took a course called Csce877.
Materials Used in this Class
Recommended AdditionalReading
DES Hints