|
Size: 1925
Comment:
|
Size: 1793
Comment:
|
| Deletions are marked like this. | Additions are marked like this. |
| Line 4: | Line 4: |
| == CPTR 427 Network Security Class == | = CPTR 427 Network Security Class Wiki = |
| Line 6: | Line 6: |
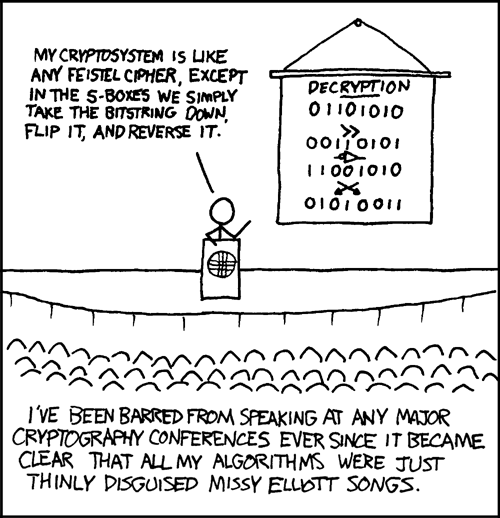
| == Labs == | {{http://imgs.xkcd.com/comics/cryptography.png}} |
| Line 8: | Line 8: |
| '''SSL and code signing lab''': | This page contains resources for Network Security CPTR 427. For assignments etc. see the [[https://eclass.e.southern.edu|Eclass website]]. For information on '''what you should already know''', take a look at [[NetworkSecurity/Prerequisites]]. |
| Line 10: | Line 11: |
| Hints: To get a code signing template to show up on the web page, you need to add it to the templates. Just go into the CA and right click templates and select new.... DO NOT ADD your site to the trusted sites list in windows. This will cause you problems. If at first you don't succeed, close it all and restart IE. | == Topics, Resources and Ideas for the future == * /NetworkSecurityEssentials4 notes from the book used in 2013. * [[/Lab]] * [[/Tools]] * [[/Programs]] * [[/Hacking]] * [[/Encryption]] * [[/Spam]] * [[/FireWall]] * [[/Topics]] * [[/SageIdeas]] * [[http://facultyfp.salisbury.edu/despickler/personal/CryptTools.asp|Cryptotools]] from AMS/MAA conference 2011 by Dr. Don Spickler. * [[http://www.backtrack-linux.org/|Backtrack Penetration Testing]] * Two proxy tools that allow editing and observing http(s) are [[NetworkSecurity/WebScarab|Web scarab]] and [[http://www.parosproxy.org/|Paros Proxy]] - there is also some nice proxies specifically for firefox. * [[http://www.securitywizardry.com/radar.htm|A nice dashboard]] * [[http://osvdb.org/|Open Source Vulnerability Database]] * [[http://web.nvd.nist.gov/view/vuln/search?execution=e2s1|National Vulnerability Database]] * Back in the stone age (relatively speaking of course) Dr. A took a course called [[Csce877]]. |
| Line 13: | Line 32: |
| '''Windows NTFS/Share Permissions Lab''' | == Books Used in this Class == |
| Line 15: | Line 34: |
| ''RSAT'' (Remote Server Administration Tools) has replaced (somewhat) the Support Tools. At any rate you can get them here: * [[http://www.microsoft.com/downloads/details.aspx?FamilyId=9FF6E897-23CE-4A36-B7FC-D52065DE9960&displaylang=en]] * [[attachment:Scriptomatic2.exe]] * [[attachment:Windows6.0-KB941314-x86_en-US.msu]] * [[attachment:rktools.exe]] |
'''Recommended Additional Books''' |
| Line 21: | Line 36: |
| ''xcacls'' has been replaced by ''Icacls'' in Vista and Windows 2008. | * [[http://www.snort.org/assets/125/snort_manual-2_8_5_1.pdf | Snort Manual]] (Free) * [[http://ofps.oreilly.com/titles/9781449320317/ch_Security.html|MVC 4 Security, Authentication and Authorization]] |
| Line 23: | Line 39: |
| == Using WebScarab with WebGoat == | == Past Year Class Pages == |
| Line 25: | Line 41: |
| 1. Start up WebScarab. It may be in basic mode. a. If it is, Go to Tools->Use Full Interface. a. Restart WebScarab. 1. Fire up IE and go to Tools->Internet Options->Connections->LAN settings. 1. Check Use proxy server and set address to localhost port 8008. 1. Click OK and OK. 1. On WebScarab go to Proxy->Manual Edit. Check Intercept Requests. Select GET and POST (using the CTRL key to select both). 1. In IE go to http://localhost./WebGoat/attack. (notice the dot after localhost, it is required to apply proxy settings on localhost.) WebScarab should already start intercepting. The lessons should work after that. I was able to do a command injection following the steps in the solution. I have now put the proxy settings back to the way they were and shut down WebGoat (for security reasons, not sure if that was necessary but I did it.) ---- CategoryHomepage |
* /Cptr427Winter2010 |
CPTR 427 Network Security Class Wiki
This page contains resources for Network Security CPTR 427. For assignments etc. see the Eclass website. For information on what you should already know, take a look at NetworkSecurity/Prerequisites.
Topics, Resources and Ideas for the future
/NetworkSecurityEssentials4 notes from the book used in 2013.
Cryptotools from AMS/MAA conference 2011 by Dr. Don Spickler.
Two proxy tools that allow editing and observing http(s) are Web scarab and Paros Proxy - there is also some nice proxies specifically for firefox.
Back in the stone age (relatively speaking of course) Dr. A took a course called Csce877.
Books Used in this Class
Recommended Additional Books
